beyond SSL - Cybersecurity. Simple. Secure.
Practical, efficient, and compliant - customized security solutions that reduce complexity and give you complete data sovereignty. beyond SSL makes cyber security accessible to all businesses.
Digital transformation brings new opportunities - but also increasing risks. In an interconnected world where cyber threats are constantly on the rise, beyond SSL stands for a pragmatic and collaborative approach that reduces complexity and ensures maximum data protection compliance. We develop customized security solutions that integrate seamlessly into your existing IT landscape - easily, efficiently, and affordably. More than 1,700 customers worldwide trust us to develop practical, future-proof solutions that are tailored to their needs in a transparent dialog. In this way, we transform complex challenges into manageable strategies while you retain full control over your data.
Why beyond SSL?
Trust through expertise
We are not just a vendor, but your trusted partner for true IT security. With in-depth expertise and years of experience, we work with you to develop individual concepts that offer real protection - without compromises and in compliance with the highest data protection standards.
Cybersecurity that thinks for you
Our innovative technologies provide effective protection that easily integrates with your existing IT infrastructure. We believe in open dialogue: We listen, analyze your needs, and partner with you to develop pragmatic security strategies that meet your day-to-day challenges-without adding unnecessary complexity.
Sustainable Security for the Future
Security is not a fixed product, but an ongoing process. We help you from initial analysis to ongoing optimization. Our customized and affordable solutions grow with your business, adapt to ever-changing threats, and ensure that you maintain data sovereignty - always in compliance with applicable privacy regulations.
Our Promise
Ready for a new era of cybersecurity?
Trust starts with the first step. Talk to our experts and find out how beyond SSL can work with you to develop customized, efficient, and future-proof security solutions for your organization - while maintaining your data sovereignty and privacy standards.
Secure remote access - at any time and completely uncomplicated.
SparkView is a remote access solution that reduces complexity while empowering your people to work more effectively and empowering your business for the long term. The Secure Remote Access Solution runs via any browser, no VPN client needs to be installed and everything runs via a server.
Secure data exchange, control and security, available from anywhere.
FileCloud is an enterprise fileshare solution designed for businesses, schools, universities, IT VARs and MSPs. It combines its core competencies of data sharing and synchronization with high usability, flexibility and productivity enhancing features.
Your specialist for remote access, FileCloud and IT security
Are you looking for a remote access solution for external access to sensitive data and critical applications? Are you looking for a cloud or IT security solution that is data privacy compliant and ensures protection against unauthorized access? With our solutions and IT security consulting services, we address precisely these requirements.
And you don't have to handle business development, channel management and digitization projects on your own. We do it for you. In close coordination with selected technology partners, we offer our customers not only reliable tools but also personal support.
During the solution selection process, we provide you with test systems free of charge at any time and support you personally with the integration into the existing infrastructure. Of course, we will continue to be there for you after successful implementation and, if desired, provide long-term support for you and your project.
All-in-one solution for authentication and authorization
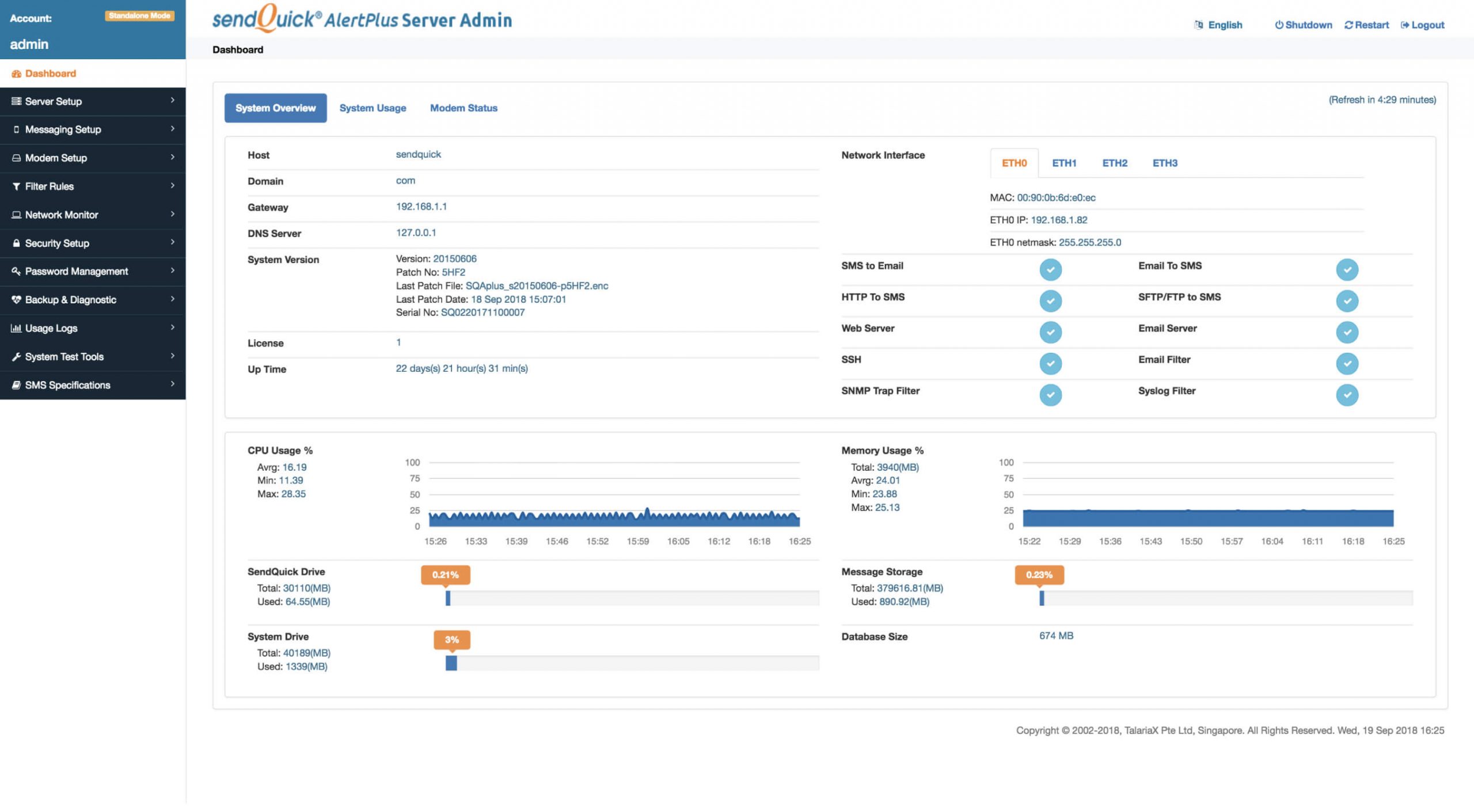
sendQuick is a series of mobile messaging solutions for enterprises. They are designed to meet critical IT requirements to minimize disruption during network downtime and ensure security and confidentiality of sensitive business data.
Create your own private office
ONLYOFFICE offers secure office and productivity apps for easy collaboration. Whether collaborative online editors with ONLYOFFICE Docs or the full suite of productivity apps for your business with ONLYOFFICE Workspace.´
Powerful hybrid work
Cloudbrink, a software-only solution, accelerates access to SaaS, UCaaS or data center apps by up to 30 times, so that mobile and remote employees in every corner of the world have a high-performance and consistent connection to their company. State-of-the-art security features ensure highly resilient connectivity, even in the event of AI-driven attacks.
Customers and technology partners
„Competent advice and fast professional support, what more could you want. The implementation was smooth, quick and easy. Coordinated appointments were kept and the discussions took place at eye level.“
Ralf Weidner„Thanks to the Proof of Concept (PoC) method, the software was installed at our company and we could immediately see how easy the program was to use. This made the decision much easier for us.“
Thoralf Geese„SparkView was the only product that integrated easily with our solution and provided the performance and stability we needed - that made it an easy decision for us.“
Eric Bégoc






























The latest from beyond SSL

What is Deception Technology – and Why is It Indispensable Today?
The world of cybersecurity is changing rapidly. Traditional defense mechanisms like firewalls and antivirus software are…

Optimal 2FA solution to complement SparkView
The SparkView remote access solution has always supported two-factor authentication and includes its own solution for…

Reports about security risks are published almost daily!
We see reports like this all the time: Vulnerability found in OpenSSH again! (1) RDP is…

